A couple of weeks ago I got a messenger popup from someone in my contacts list. Quite innocuously suggesting that they had seen a picture of me they asked me to confirm by clicking on the link. As it was a contact I trusted I dutifully complied. Dumb.
The link contained a Win32/RCBot.ADH Trojan which my local NOD32 install picked it up but several other contacts also received the same link (although not, thankfully, sent from my computer). That got me to thinking, I use Squid-cache to cache and forward on my Local Area Network. It’s a useful service, especially as I do hit the same sites quite often. I’d played with add-ons for Squid in the past, Dansguardian, Squid-Guard, etc and had tinkered with c-icap before but never got it to compile properly. Other things just took precedence.
I decided to revisit it, eventually being strangely surprised and happy to find it wasn’t so bad to work the problems out after all.
For those who don’t know, you can AV Scan web content (both http, ftp and https) using Blue Coat’s ProxySG/AV products. It’s an extremely powerful solution for a company wanting to both enforce AUP’s and ensure that the content that IS allowed is virus-free. The AV solution supports different AV engines (Kaspersky, McAfee, Sophos to name but a few) with the AV appliance. It’s a nice product to work on and very diverse in application and deployment. But not something you can afford for home…..unfortunately :)
The ProxyAV uses the ICAP protocol (Internet Content Adaptation Protocol) to pass inbound content (html objects, file downloads, etc) to the installed AV scanner. From there, it’s scanned and assigned a token (good or bad) and the token returned to the ProxySG telling it to either serve the content to the user or not as the case may be. It’s quick and gets the job done very well.
The Open Source alternative to such a system comes in the form of c-icap, ClamAV and Squid. C-icap acts as a ‘channel’ for web content from Squid-Cache to be passed through to the AV Engine (ClamAV). The content is then scanned and the control token sent back to Squid-Cache to either allow or deny.
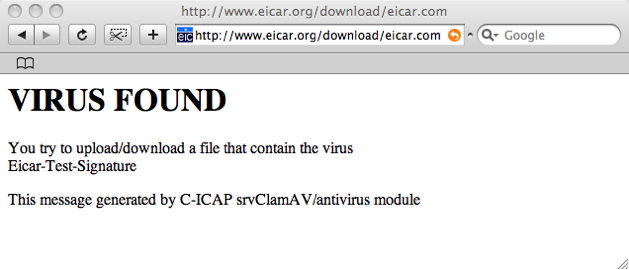
This is what you get if you inadvertently walk into a virus.
Nice, and I bet you can beautify the page content :)
So, to install it, here’s what I did. I’ve performed the installation on Debian (Edgy) and Ubuntu (6.10LTS) and both work. Debian was on a MIPS Cobalt Raq2, Ubuntu on an i386 server. MIPS was a little slow to load the service but worked, the i386 box (which also runs Squid) flew, especially redirecting the content to an already active ClamAV network service on the box.
I used the following configuration options from the c-icap.conf example file (and checking the MAN pages).
PidFile /var/run/c-icap.pid CommandsSocket /var/run/c-icap/c-icap.ctl Timeout 300 KeepAlive On MaxKeepAliveRequests 100 KeepAliveTimeout 600 StartServers 3 MaxServers 10 MinSpareThreads 10 MaxSpareThreads 20 ThreadsPerChild 10 MaxRequestsPerChild 0 Port 1344 User root Group nobody TmpDir /var/tmp MaxMemObject 131072 ServerLog /usr/local/var/log/server.log AccessLog /usr/local/var/log/access.log ModulesDir /usr/local/lib/c_icap Module logger sys_logger.so Module perl_handler perl_handler.so sys_logger.Prefix "C-ICAP:" sys_logger.Facility local1 Logger file_logger acl localnet_options src 192.168.17.0/255.255.255.0 type options acl localnet_respmod src 192.168.17.0/255.255.255.0 type respmod acl localnet src 192.168.17.0/255.255.255.0 icap_access allow localnet_options icap_access allow localnet_respmod icap_access allow localnet ServicesDir /usr/local/lib/c_icap Service echo_module srv_echo.so Service url_check_module srv_url_check.so Service antivirus_module srv_clamav.so ServiceAlias avscan srv_clamav?allow204=on&sizelimit=off&mode=simple srv_clamav.ScanFileTypes TEXT DATA EXECUTABLE ARCHIVE GIF JPEG MSOFFICE srv_clamav.SendPercentData 5 srv_clamav.StartSendPercentDataAfter 2M srv_clamav.MaxObjectSize 5M srv_clamav.ClamAvTmpDir /tmp srv_clamav.ClamAvMaxFilesInArchive 0 srv_clamav.ClamAvMaxFileSizeInArchive 100M srv_clamav.ClamAvMaxRecLevel 5
You can have a play around with the settings to suit your needs but for my home network, as complex as it can be sometimes ;0), it’s enough.
1. Have your server installed with the following additional packages installed via apt-get –
apt-get install clamav-daemon gcc make automake binutils unzoo libc6 libc5-dev unrar lha
(agree to any dependencies). ClamAV will need to be configured to run as a network socket, not a ‘unix’ process.
2. Download c-icap from SourceForge and un-tar/gzip it in your directory of choice (/tmp for example) – tar xzvf c_icap*.tar.gz
3. cd c_icap<version>
4. ./configure –with-clamav
5. make
6. make install
7. Edit /usr/local/etc/c-icap.conf and make your required changes. For your own network, you’ll need to change it to suit your needs. Such as
acl localnet_options src 192.168.17.0/255.255.255.0 type options acl localnet_respmod src 192.168.17.0/255.255.255.0 type respmod acl localnet src 192.168.17.0/255.255.255.0
…and
srv_clamav.VirHTTPServer "http://path.to.server/path/to/get_file.pl?&remove=1&file="
You’ll need to copy the ‘get_file.pl’ script from the /contrib/ directory of the c-icap tar file to a local web service (Apache) in order to make the above command option work in a browser (it’s what is required to display a link to the download file once ClamAV has finished scanning it).
8. If you want to run the program in debug mode to begin with (recommended) you can run the following command – c-icap -N -D -d 10 -f /path/to/c-icap.conf – where you can observe the output for problems.
9. Next, you can use the built-in ‘icap-client’ command to confirm the service is working. Download the eicar.com file from eicar.org to your server.
icap-client -f /path/to/eicar.com -d 10
You should get the following in the /usr/local/var/logs/server.log
Take action…….
Mon Feb 18 22:56:30 2008, general, VIRUS DETECTED:Eicar-Test-Signature.
10. Once this is done and is successful you need to tell Squid to redirect connections to the c-icap service. This is done with the following:
icap_enable on icap_preview_enable on icap_preview_size 128 icap_send_client_ip on icap_service service_avi_req reqmod_precache 0 icap://localhost:1344/srv_clamav icap_service service_avi respmod_precache 1 icap://localhost:1344/srv_clamav icap_class class_antivirus service_avi service_avi_req icap_access class_antivirus allow all
If you’ve have a version of squid that doesn’t support ICAP you’ll get an error in syslog such as –
squid: parseConfigFile: line 4296 unrecognized: ‘icap_enable on’
If this happens, you’ll need to grab a new copy of Squid from the Source and compile it with the ‘./configure –enable-icap-support’ command.
11.Once you have Squid running with ICAP support you can re-run the Squid Daemon along with c-icap. C-icap can be started with – c-icap -f /path/to/c-icap.conf – if you’re finished with debugging that is :)
Squid will log as normal to it’s access_log, c-icap will log to /usr/local/var/log/server.log. Keep an eye on them if you have any issues retrieving pages or suffer any errors at startup. I’m going to keep an eye on mine for the next couple of weeks as I play around with the settings.
Compared to the power of the ProxyAV from Blue Coat, this isn’t a competitor. The code it still in development. For someone like me who likes to tinker, it’s a useful service to have. Not that I visit the sites that contain viruses (of course) ;) but to help cover the possibility of an infection from the web.
You could run it on a company network if you ‘really’ want to but it may consume precious administration time if things go wrong. If they do, you can simply disable the rule in your squid.conf file until you figure the problem out (icap_enable no instead of yes) but it’s your call :)
Happy, safe, virus-free surfing!
PS: I consider this service very useful. There are possibilities of using is in ‘Reverse Proxy’ mode with Apache’s proxy_engine or even Squid’s reverse proxy capabilities. What about a cluster of c-icap boxes load-balanced via Riverbed Stingray Traffic Manager? I’ll be keeping an eye on the progress of it’s development with interest.